
Is Web Mining Still A Thing?
You could be mining and not even know it
Last Wednesday, French police shut down a massive botnet that managed to install malware on over 850,000 computers. This network was partially used to distribute ransomware and carry out data theft. However, it was also used for cryptojacking, allowing the attackers to mine Monero on their victims’ computers.
The three-year-long operation earned the attackers millions of dollars worth of crypto. Although the exact figures are still unclear, cryptojacking is a growing trend. In fact, Kapersky reported earlier this year that corporate traffic pertaining to crypto mining has grown by 200 times over the past year – and cryptojacking is mostly to blame.
However, web mining scripts, which are often used by cryptojackers, are not doing nearly as well. These scripts allow website operators to mine cryptocurrencies using the CPU power of visitors to the site.
CoinHive, one very popular script, shut down earlier this year due to falling profits and continuous changes within Monero’s mining scheme. This has left cryptojackers with one less tool at their disposal, and now, they are being forced to seek out alternatives.
The New Web Miners
Several different mining scripts are readily available, and it’s easy to see which scripts are most popular. PublicWWW allows us to search for code snippets, a technique that Binance Academy and Bad Packets Report have used to identify popular mining scripts in the past. This shows us how many sites are hosting each particular mining script, as shown below:
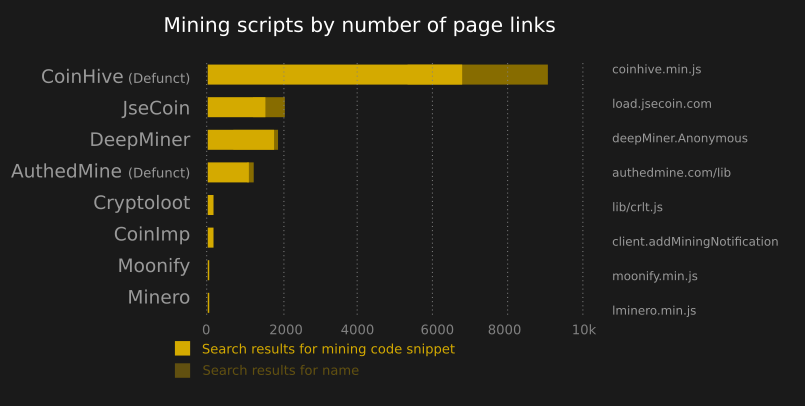
Despite its shutdown, CoinHive still seems to be leading the race. Bad Packets says that CoinHive was active on 30,000 sites in late 2018, and Binance says it was active on 15,000 this February.
Even today, at least 6000 sites still attempt to use CoinHive. The most likely explanation is that many sites simply haven’t been updated since CoinHive shut down.
Meanwhile, there are also alternative mining scripts, which require users to consent to mining. JSECoin is used by at least 1500 sites, and it only mines if visitors opt-in. AuthedMine, an opt-in miner created by CoinHive, is present on at least 1000 pages, though it is now defunct.
Other scripts are a mixed bag. DeepMiner is present on at least 1750 sites. CoinImp is present on at least 100 sites, though this figure is easy to underestimate, since its embed code is difficult to pinpoint. Finally, Cryptoloot and Moonify have a very minor presence, and can be found on roughly 20 pages each – still, they are viable tools for web mining.
Are You Being Crypto-jacked?
This data merely represents run-of-the-mill attempts at web mining, and does not reflect if there are any large-scale attacks are underway. Many of the sites found on PublicWWW are merely run by web operators who use your computer’s power to mine crypto for the duration of your visit.
Although cryptojacking can be a minor nuisance, it is rarely dangerous on its own.
In fact, these data probably don’t show any elaborate attacks. In 2017, for example, attackers injected mining scripts into Starbucks’ private wi-fi networks. Later, in 2018, attackers injected a script into text-to-speech software, which reached 4000 government websites at once. If similar attacks are underway today, there might be no way of knowing.
Furthermore, our data doesn’t show which crypto miners have been hitting website visitors the hardest – it only shows how many websites use the mining scripts. It’s possible that some scripts are popular with website operators whose websites that receive a lot of traffic. Additionally, some scripts don’t mine at full power, or allow this to be adjusted.
Based on these figures, web mining and cryptojacking are both likely on the decline. A recent study shows that profits are quite modest, and that the average cryptojacker earns about $5.80 per day per website. As such, it seems that cryptojacking’s growth might be due to its enticing image, not its actual profitability.

 Earn with Nexo
Earn with Nexo