
Bitcoin Wallets were Letting People Get Scammed with Faulty Balances
A bug in three major cryptocurrency wallets let people get duped by double-spent Bitcoin.
A bug in three major cryptocurrency wallets let scammers dupe people with double-spent Bitcoin, allowing unconfirmed transactions to count in a user’s total wallet balance.
Unreliable Bitcoin Wallet Balances
The technical gap makes it possible for attackers to trick users of vulnerable Bitcoin wallets into believing that they had received Bitcoin, even if the transaction wasn’t confirmed.
Before a Bitcoin transaction can be considered final, it is necessary to wait up to several hours before the transaction is considered irreversible. The more confirmations the transaction gets, the harder it becomes to override that transaction with higher fees.
Most Bitcoin veterans check for the number of confirmations on a transaction before considering it final, but new users can easily be duped by seeing an artificially inflated wallet balance.
Several popular Bitcoin wallets, including Ledger Live, BRD wallet, and Edge, were susceptible to this vulnerability.
The RBF (Replace-by-fee) feature on the Bitcoin network allows senders to have their unconfirmed transactions replaced by another transaction, which would replace a previous transaction with one with a higher fee. Bitcoin miners would then pick the transaction with the higher fees, essentially replacing the previous transaction.
Some wallets had a hard time implementing RBF correctly, which ultimately resulted in the appearance of BigSpender, a family of vulnerabilities that include double-spending and multiple-spending attacks. Hence the name “BigSpender,” which lets attackers spend more than what they have, often to scam people.
Bitcoin Core version 0.12 implemented RBF, which explicitly put the responsibility of verification on users for confirming transactions themselves based on the number of confirmations.
The vulnerability allows wallets to update their balances with unconfirmed transactions. The result—balances on major wallets were no longer a source of truth for recipients, and instead represented potential transactions waiting to be processed.
Bitcoin transactions are represented by a series of “state” changes. Bitcoin transaction, like any other transaction, is a journey from the initial state to a final state with intermediary steps.
When a user initiates a transaction, it’s the initial stage. When the transaction spends time in the mempool waiting for confirmation, it is in an intermediate state. Finally, when the transaction is confirmed, it enters its final state.
When someone initiates a new transaction with a higher fee, the state of a transaction goes from the intermediate state to the initial state for the first transaction. These wallets were incorrectly considering the intermediate state as the final state when calculating wallet balances.
RBF misconfiguration in wallets allows malicious actors to execute several BigSpender exploits—double-spend attacks, amplification attacks, and denial-of-service (DoS) attacks.
An amplification attack is when a scammer repeatedly sends the same small amount of Bitcoin over and over to deceive someone into believing they had actually received a large amount of Bitcoin. For example, 100 failed transactions of $5 would inflate a wallet balance by $500. These kinds of tricks make it easy to dupe new Bitcoiners.
Wallet Companies Warned to Fix the Issue
These vulnerabilities were first disclosed to these three wallet companies by ZenGo, an Israeli cryptocurrency wallet. “In some of the vulnerable wallets, this attack is hard (or even impossible) to recover from,” said ZenGo.
ZenGo released the report after giving the wallets 90 days to remedy the issue. The company received bug bounties from Ledger Live and BRD wallet, while Edge acknowledged the vulnerability and said they planned on fixing it in the future.
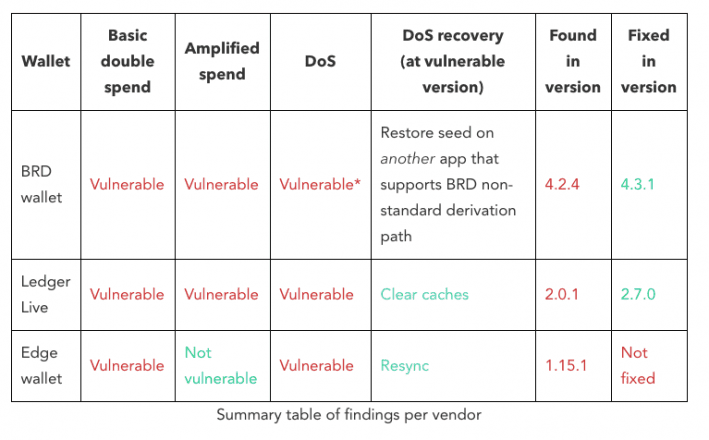
BRD and Ledger have patched their code, but Edge wallet is yet to fix it. In the future, cryptocurrency wallets must remain diligent about the nuances of the Bitcoin blockchain to prevent people from getting taken advantage of.

 Earn with Nexo
Earn with Nexo