
Perlin Code Review: Avalanche DAG
Andre Cronje's Perlin code review suggests that that their blockchain protocol represents a "new paradigm" and is "terrifyingly good".
Perlin code review, enjoy it while it lasts because I have two projects on my plate right now that I’m probably not going to like at all. So what is this thing, anyway? Decentralized computing, good but lots of it around, scaling for dApps, good but lots of it around, privacy as well, good but lots of it around.
Thought I was missing something at first, all the hype around Perlin, had to get into the code to see why this was generating so much noise. Actually, it IS Noise partly, but will get to that in a minute.
Full ICO review is here, anyway.
Off we go, Perlin code review.
“High-throughput privacy-preserving compute network”
“Perlin Network is building a scalable privacy-preserving general compute network, incentivized with a mineable coin: PERL”
“…provides on-demand access to aggregated batches of compute machines around the world…”
“…resource-lock proofs representative of a miner’s CPU time and RAM invested into a client.”
Decentralized compute-as-a-service, lots of competitors currently in this space.
So, what are they trying to achieve? Decentralized cloud-computing where you rent out computing resources for whatever your needs may be. In AWS we have EC2 (or ECS) where we rent (for example) 8 gigs of RAM and 4 CPU’s.
In a current decentralized network we can give compute jobs, but we can’t know that we are getting 8 gigs of RAM and 4 CPU’s. Perlin proposes to address this by having cryptographically secure proofs of the RAM and CPU being made available.
Let’s jump into the whitepaper.
Usual pitch, allow access to underutilized computing resources. They propose resource-locks, “which is an asymmetric memory-hard cryptographic hash function to quantitatively determine that supplier truly holds some amount of computing resources”
The paper continues to go into the math of resource-locks, going to try to ELI5 it.
What do resource-locks want to prove? How much memory and CPU is available (and inversely if I know the above, how much memory and CPU are in use). It does this via a cryptographic stress test that pushes memory and CPU to its limits, doing this gives us max memory and max CPU. Now if the system is currently being used I can do this again and then I know the load used. By doing these at random intervals over time you begin having a averaged amount of memory and CPU available, which means you can start securing these resources.
This is a very nice touch, since now if I need 32 gigs of RAM for some memory intensive computing requirement I know the provider has the resources I require. Starting to look sexy;
HashGraph, so they are building their own blockchain. “…three major components being a self-audited distributed ledger, a cryptographic proof of computational resources, and a framework for highly parallel blind computing.” Whitepaper is a bit confusing, let’s jump into code;
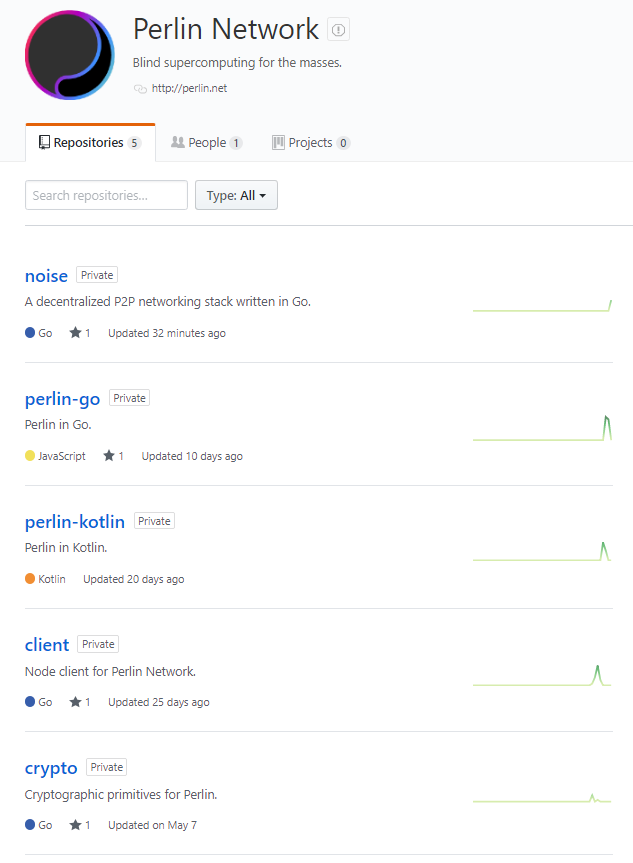
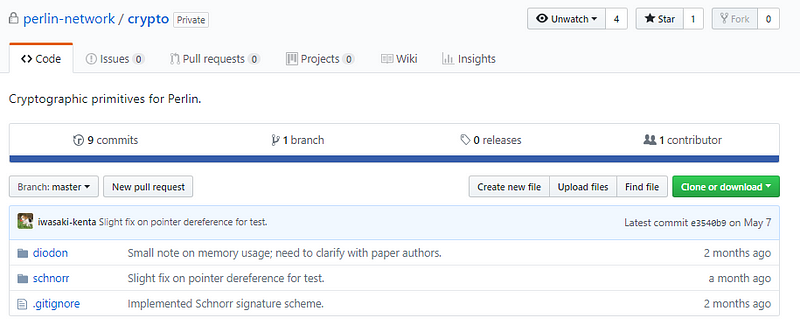
I’m excited to see so many repo’s on a pre-ICO project. Let’s jump into crypto.
(The team specifically asked me not to post the code for resource-locks, it is their secret sauce after all.)
RSA, memory-hardness, time complexity. Resource locks straight forward, only 15 lines of code, but it is elegant. Given the parameters M and L it can ascertain the available memory and cpu. Nice to see such a clean implementation. Their resource lock isn’t theoretical, it is already a working version.
Let’s grab another repo (Noise). See, I got to it.
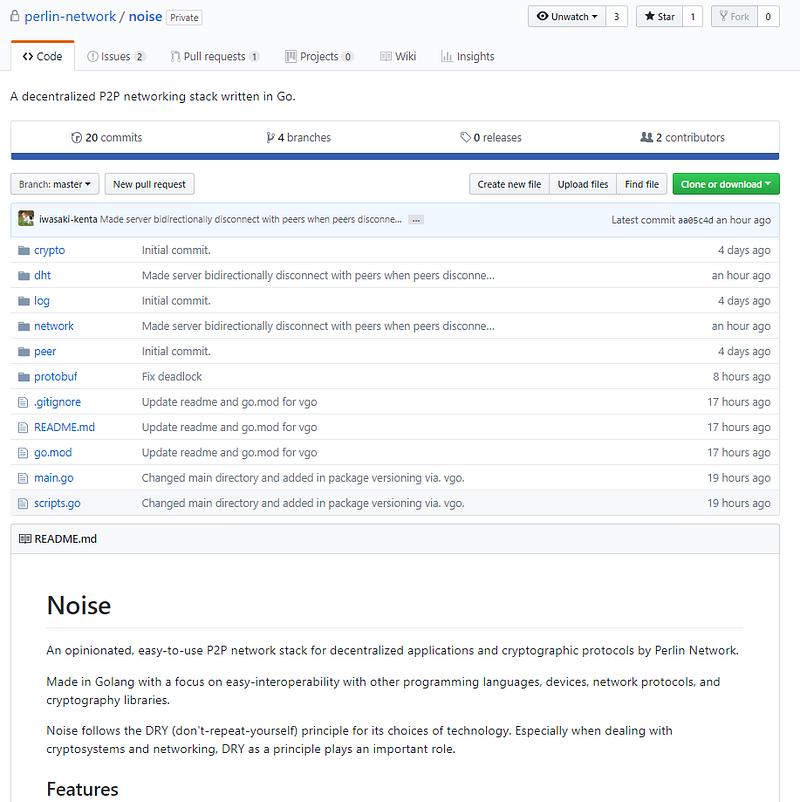
“An opinionated, easy-to-use P2P network stack for decentralized applications and cryptographic protocols by Perlin Network” hehe, I like the opinionated 🙂
So, this is a real-time, bidirectional streaming p2p protocol using gRPC and Protobufs, I’m always happy to see gRPC and Protobufs, they have been thoroughly developed and tested, so why do we keep reinventing the wheel? (I say while looking at Perlin’s own reinvention of P2P)

Straightforward, let’s jump into crypto and network.
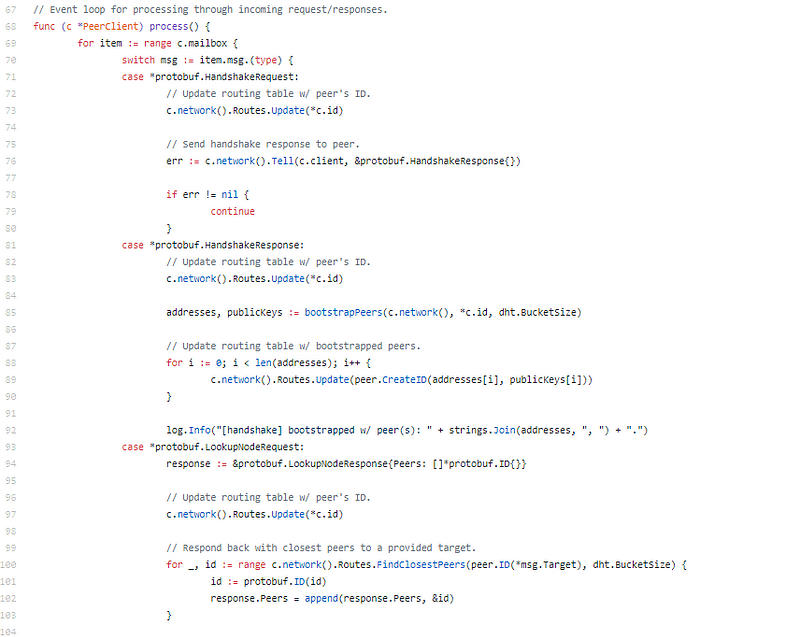
Request-response using protobuf
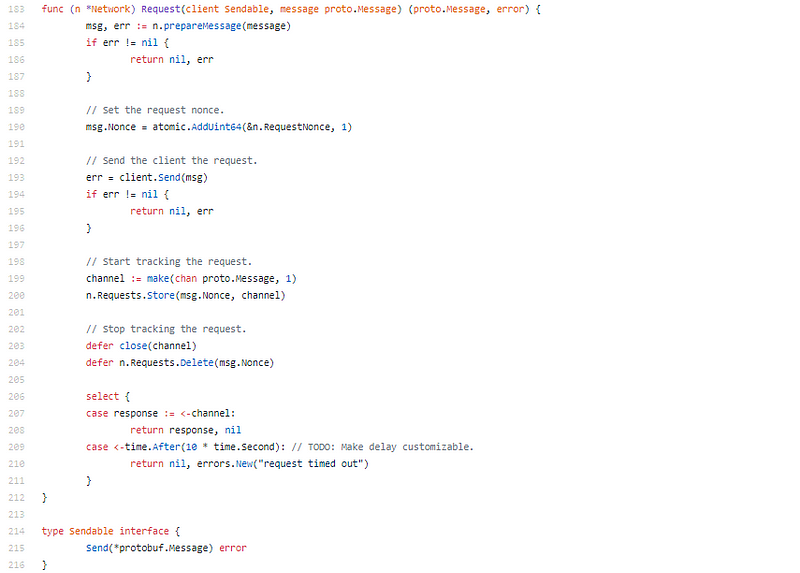
There is something annoying elegant in this code. Everything is just so concise and neat and at the same time reads and flows so beautifully. It’s weird, it’s both KISS (Keep It Stupid Simple) and complex.
Noise is a simplified, easy to implement p2p lib and its designed in a modular and elegant way. I’m going to fork this.
Ok, so Noise is sexy, and resource-locks solid. Next we have client, perlin-go, perlin-kotlin, let’s jump into perlin-go
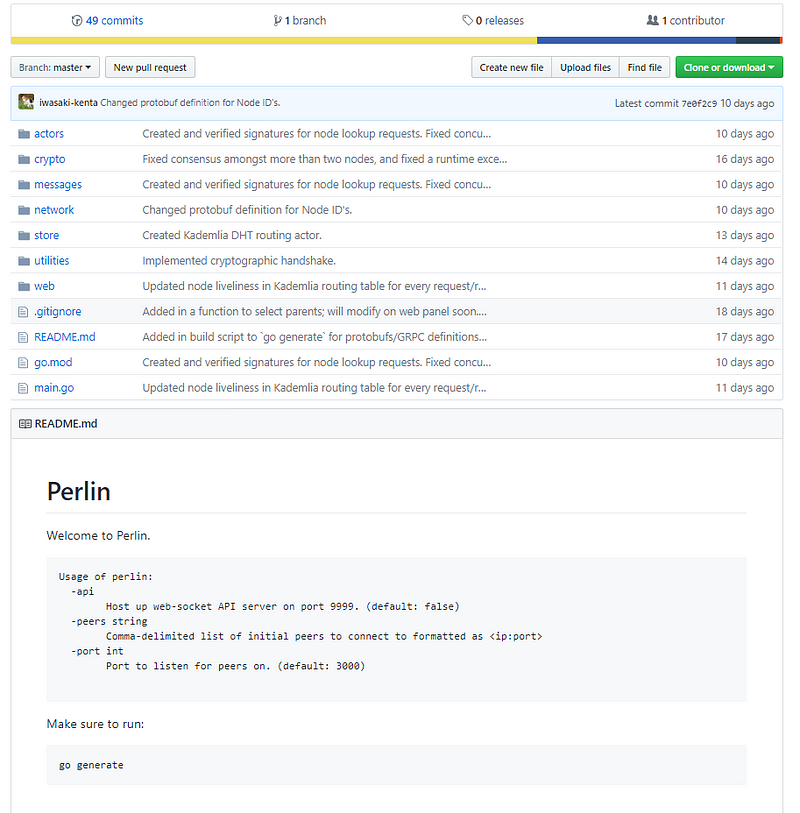
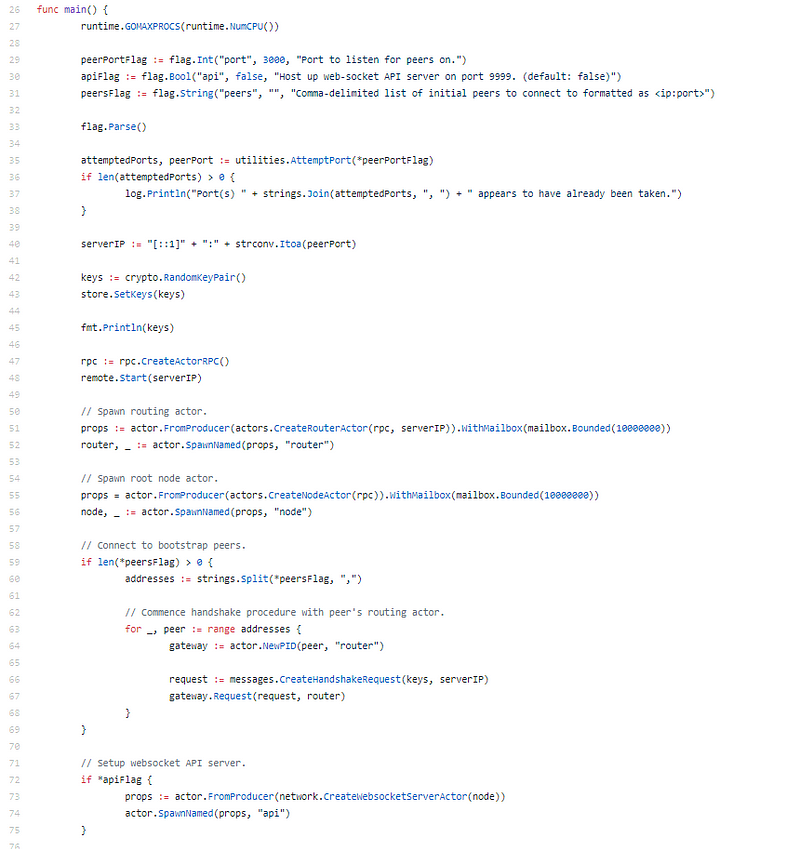
This is a ground up build, not a fork. They implemented noise and an API server.
Actor model used, this is a functional programming pattern, allows for a lot of asynchronous behavior. I don’t often see the actor pattern in blockchain projects. I really like the actor pattern. (No Mutex’ required)
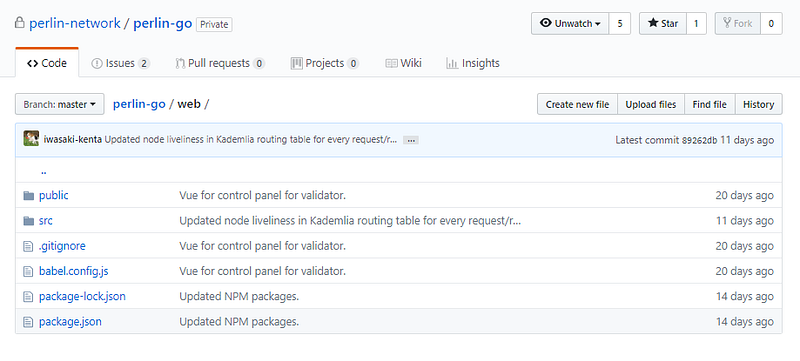
Web is a Vue front-end, let’s come back to this later.

Websockets, straightforward.
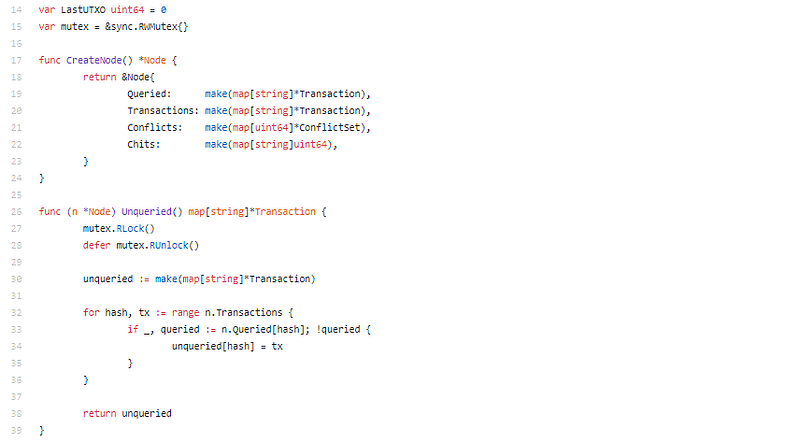
UTXO based model?
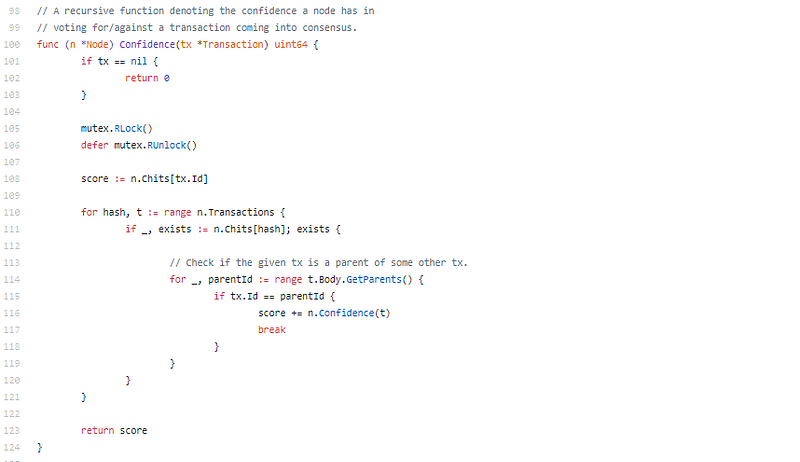
Confidence rating on transaction for consensus.
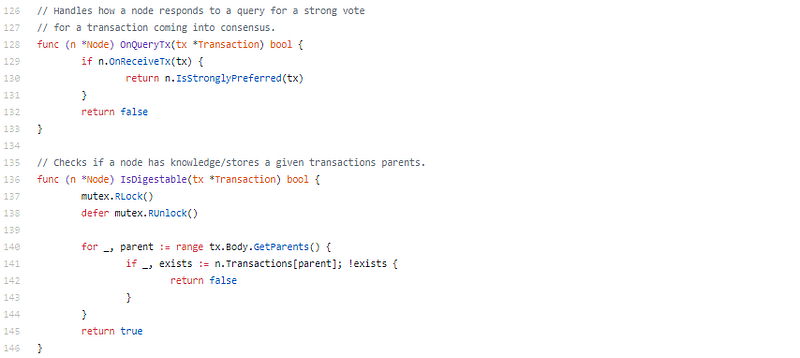
Mmm? OnQueryTx, strong vote, knowledge/stores a given transactions parents? This is Snowflake, Snowball, and Avalanche.
What? They implemented Avalanche…
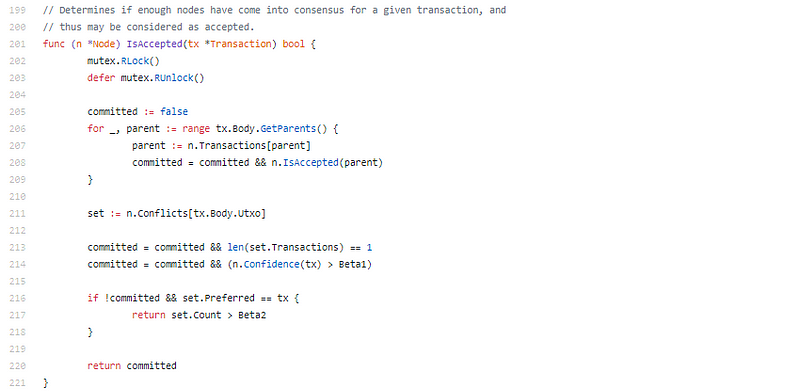
It’s Avalanche. I’m struggling to believe this, resource-locks, Noise, now Avalanche. I don’t really know where to go from here, just continuing with the code seems kind of pointless, this is fantastic. As in unbelievably good. What do I do next? Just post another code snippet and comment “they used nice comments”. I’m at a loss for words.
…
…
OK I’m back.
So, I went through the rest, perlin-kotlin, a Kotlin implementation of their Avalance DAG. (That they did just for fun to do some Kotlin)
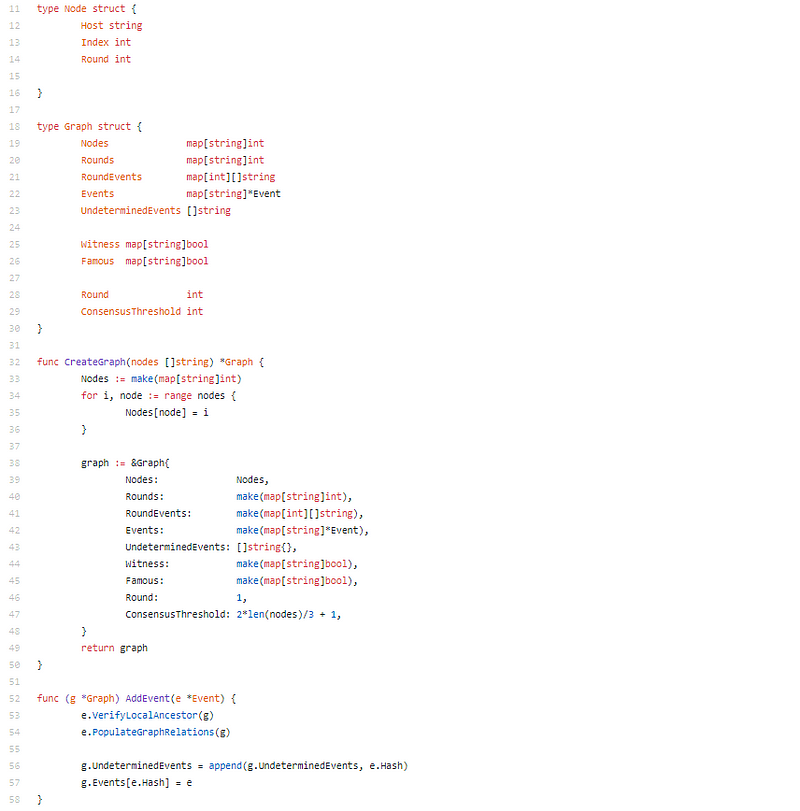
Did I mention they also have a HashGraph and round implementation? But it looks like they moved over to Avalanche now.
Seriously, this is amazing.
Perlin Code Review Conclusion:
I don’t know, this is terrifyingly good. I’m fairly confident in my developer capabilities, and this outplays me. All of this work in 3–4 months. I’m terrified to see what these guys are going to accomplish. This isn’t just a compute-as-a-service platform, this isn’t just an AWS EC2 competitor, this is a new paradigm.
I seriously don’t know, I’m at a loss for words. I want to work with these guys.
This is as good as I’ve seen in quite a while.
A full review of the Perlin ICO by our analyst team can be found here.
Disclaimer: Crypto Briefing code reviews are performed by auditing what is on display in the master branch of the repo’s made available. This was performed as an educational review and any comments in the article are the opinion of the writer. It is normal for code to change rapidly, hence we timestamp our code reviews so that they present a snapshot at a moment in time. Information contained herein should not be used as any comment or advice on the project as a whole.
Perlin Code Review Timestamp: June 17th, 2018 at 20:28 GMT

 Earn with Nexo
Earn with Nexo